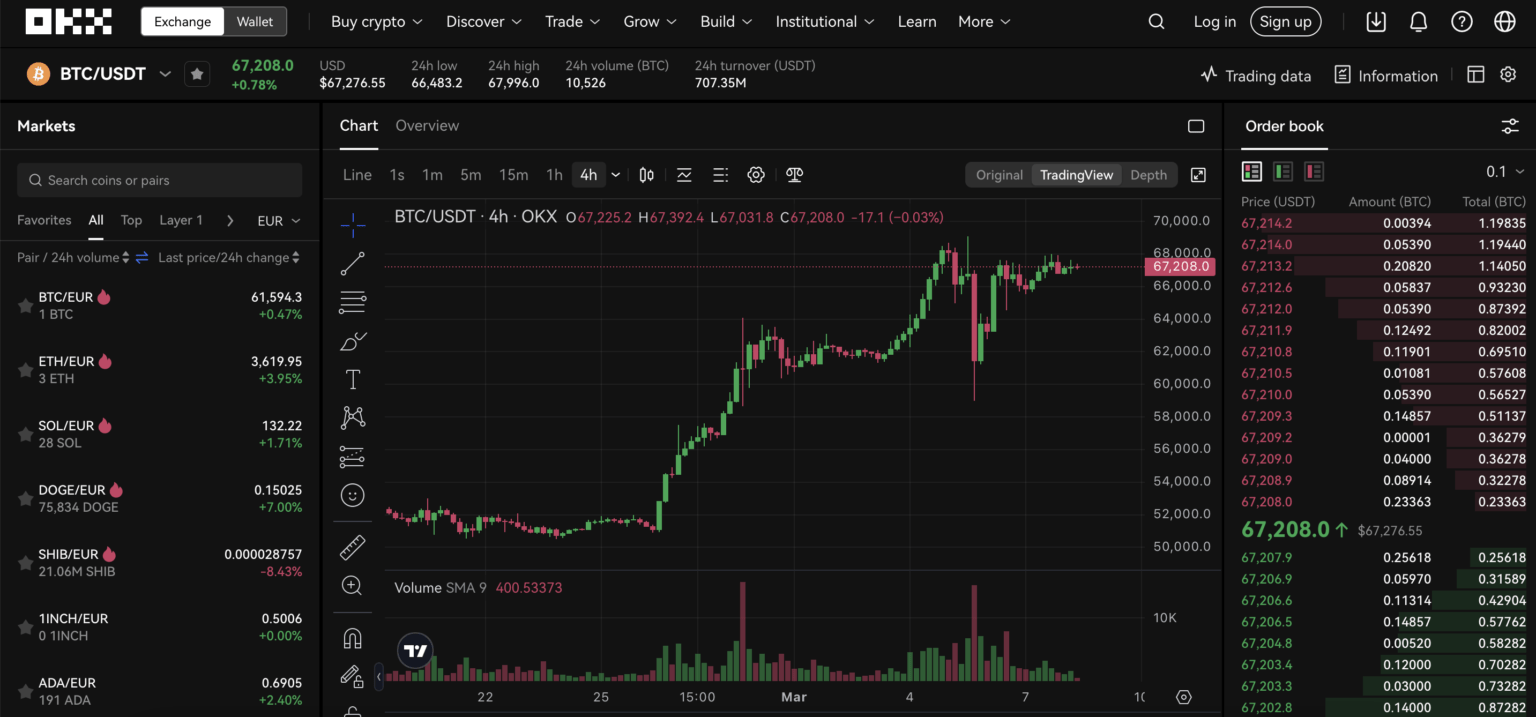
Surprising fact: a secure login is not a single event but a distributed process spanning on-chain proofs, cold storage policy, biometric sensors, and human behavior. Many US traders treat “signing in” to an exchange as a momentary convenience — enter password, get market access — but with platforms like OKX the authentication pathway is a multi-layered system whose design choices shape liquidity access, custody risk, and regulatory friction.
This article unpacks how OKX’s sign-in mechanisms interact with custody models (centralized exchange vs non-custodial wallet), how KYC and 2FA affect your operational freedom, and where the common misconceptions break down. You will leave with a clearer mental model for deciding how to split funds, when to use the web platform versus the Web3 wallet, and what to watch for in future changes.
How OKX Sign-In Actually Works: the mechanism behind the screen
At the core, OKX combines three linked subsystems that traders confuse: account authentication, custody domain, and device/credential management. Authentication is the path by which the exchange verifies “you” — typically a username or email + password, then mandatory Two-Factor Authentication (2FA) via SMS, Google Authenticator, or biometrics. That 2FA step is not extra friction for fun; it’s an enforced second factor that drastically reduces remote account takeover risk, but it does not eliminate phishing or social engineering.
Custody domain matters because OKX operates both as a centralized exchange (CEX) and provides a non-custodial Web3 wallet. Logging into the OKX web platform gives you access to your on-exchange balances (custodial) and trading features like spot, margin, and derivatives. Separately, the Web3 wallet is self-custodial: your seed phrase or hardware wallet controls keys. The login methods and recovery options differ sharply between those domains — losing the seed phrase for a Web3 wallet can mean irreversible loss, whereas locked access to a custodial account is a customer-service problem that can be remedied (slowly) through KYC.
Device and credential management bridges those worlds. OKX supports biometric login on mobile and maintains AI-driven session monitoring for suspicious logins. This means the platform will flag unusual device signatures or IP patterns and may require re-authentication. Those protections are effective at scale, but they create false positives for frequent travelers, VPN users, or traders who deliberately switch endpoints for privacy. Understanding how these three subsystems interact helps you choose the right operational pattern: which balances convenience, custody, and recoverability.
Common Misconceptions — and the reality traders should use
Misconception 1: “2FA is bulletproof.” Reality: 2FA reduces risk but can be bypassed via SIM swapping, phishing that captures codes in real time, or social engineering that abuses support channels. For US-based traders, prefer app-based authenticators or hardware-backed biometrics over SMS where possible.
Misconception 2: “If OKX says it’s insured or keeps assets cold, my funds are safe.” Reality: OKX does store over 95% of assets in multi-signature, air-gapped cold wallets, but operational risk and non-custodial DeFi interactions expose you to smart contract exploits and protocol risk. Proof of Reserves provides an extra transparency signal, but it is not insurance against market loss or all operational failures.
Misconception 3: “The Web3 wallet is the same as my exchange account wallet.” Reality: they are different custody regimes. The Web3 wallet gives control and responsibility — you manage the seed phrase, and integrating a hardware wallet like Ledger or Trezor is strongly recommended for large holdings. The exchange wallet is convenient and supports staking, margin, and high-frequency trades — but custody means counterparty risk and the need to trust KYC procedures and withdrawal controls.
Practical trade-offs: login choices and money management frameworks
Here are concrete frameworks you can reuse.
1) The Three-Account Model (decision-useful heuristic): keep funds split across (A) Hot trading account on OKX for active positions and margin use, (B) Staking/Yield account on OKX for flexible/fixed staking and auto-compounding rewards, and (C) Cold or self-custodial wallet (hardware-backed) for long-term holdings and risky DeFi experiments. Each account has a different sign-in and recovery profile: A and B rely on KYC + 2FA, C relies on seed phrase + hardware device.
2) Access minimization rule: enable the minimal set of login options you need. For example, if you never use mobile trading, avoid mobile biometric login to reduce the attack surface. Conversely, if mobile is your primary execution device, bind biometric login with a hardware-backed authenticator as an additional safeguard.
3) Staged withdrawal plan: when preparing to move large amounts, initiate small test transfers between custody domains to verify your signer, chain choice, and withdrawal whitelists. Do not assume cross-chain bridge aggregators will always select the cheapest or safest route; check the route and counterparty risk before approving swaps.
Where the system breaks: limitations and attack surfaces to monitor
Account login is a prerequisite, not a guarantee. The main failure modes are phishing, SIM-swap, social-engineering of support staff, and self-custody mistakes (lost seed phrase). For US users, KYC introduces both friction and recovery options: if you are locked out of custodial access, KYC allows an administrative path to restore control — but that path can be slow and requires identity documents and liveness checks.
DeFi interactions via the OKX Web3 wallet create a different class of risk: smart contract bugs and malicious approvals can drain funds regardless of how secure your login is. Multi-layered defense means separating the signing key (hardware wallet) from the day-trading account and limiting token approvals when interacting with DApps.
Operationally, the exchange periodically delists low-volume or high-risk spot pairs (recently RSS3, MemeFi, GHST, RIO, SWEAT were delisted), which can affect liquidity for positions you hold. Sign-in functionality will not protect you from poor liquidity when a pair collapses; account access helps you exit, but it doesn’t change market mechanics.
How to sign in securely right now — step-by-step heuristics
1) Prepare: register with a unique, high-entropy password and enable an app-based 2FA (Google Authenticator or a hardware token). Reserve SMS 2FA only as a fallback.
2) Bind devices: when you first sign in on desktop, consider adding a withdrawal whitelist and device fingerprinting. On mobile, enable biometric login but pair it with a separate authenticator app and, where supported, a hardware security key.
3) Verify recovery paths: ensure your custodial account has up-to-date KYC and contact methods; separately, store your Web3 seed phrase offline in at least two secure locations or on a hardware wallet.
4) Test small: before transferring meaningful funds between domains (e.g., from exchange to self-custodial wallet), perform a small transfer and confirm address and chain compatibility, especially when using DEX aggregators or bridging tools.
What to watch next — signals and conditional scenarios
Monitor these trends because they materially affect sign-in and custody choices:
– Regulatory pressure in the US on KYC/AML could push exchanges to tighten identity controls, increasing recovery capability but making anonymous access harder. If regulation intensifies, expect stricter liveness checks and longer manual review times.
– Adoption of hardware-bound authentication (passkeys, FIDO2) would reduce phishing risks; if OKX moves to broader passkey support, prioritize those options. Conversely, if SMS remains widely supported, keep treating it as second-best.
– Changes to token listings (delistings) signal liquidity maintenance; a wave of delistings is a market-safety mechanism but increases the importance of having access and redundancy in sign-in options during rebalances.
FAQ
Q: Is the OKX Web3 wallet the same as signing in to OKX exchange?
A: No. Signing in to the OKX exchange accesses a custodial account protected by KYC, two-factor authentication, and the exchange’s custody controls (including cold storage). The Web3 wallet is non-custodial: you control the private keys and seed phrase. Each has different recovery methods and risks; mix them intentionally rather than assuming one covers the other.
Q: If I lose access to my OKX account, how do I regain it?
A: For custodial accounts, recovery usually proceeds through KYC validation (government ID, liveness check) and support verification. That process can be slow but is possible. For non-custodial Web3 wallets, losing a seed phrase typically means permanent loss — there is no support channel to restore keys. Plan backups accordingly.
Q: Which 2FA method should I choose?
A: App-based authenticators (time-based tokens) or hardware security keys are preferable to SMS because they resist SIM-swap attacks. For US traders who travel, couple an authenticator app with device whitelisting or hardware tokens to reduce service interruptions from travel-related login flagging.
Q: Does OKX proof of reserves mean my money is insured?
A: Proof of Reserves provides transparency about on-chain backing, which is valuable but not the same as insurance. PoR shows the exchange holds assets corresponding to user balances, but it does not cover market losses, smart contract failures when you interact with DeFi, or certain operational contingencies.
Final practical step: if you plan to trade actively, bookmark the official sign-in help and practice a staged approach to access and custody. For a direct route to the OKX web sign-in flow and platform guidance, use this link to ensure you are on the supported login page: okx login. Treat sign-in not as a nuisance but as the first line of portfolio defense.